As a system admin, you need to be able to communicate with other systems on a network to share data. You can do so using the ssh command in Linux. It is a command-line utility in Linux systems which connects your system to a remote host.
What is SSH?
The ssh utility stands for ‘Secure Shell’. It is a data transfer protocol designed to securely encrypt and transmit data between two systems.
It encrypts data for transmission using three main methods: symmetrical encryption, asymmetrical encryption and one-way hashing. These prevent your data from being leaked. Further, it helps verify the authenticity of the data you receive. By default, ssh connections are formed at port 22 using TCP/IP.
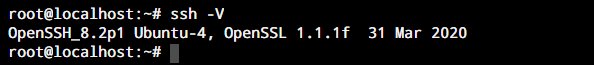
The Ubuntu 18.04 default repository comes preinstalled with the OpenSSH client package. We will verify it by typing the following in our command line.
ssh -V
If you see an output similar to the following, you have the OpenSSH client installed on your system.
If it is absent, the OpenSSH package can easily be installed by entering the following in your terminal:
sudo apt install openssh-client
Once the installation is complete, you can follow the rest of the tutorial. We use apt instead of apt-get based on the recent update to the command. The apt command is more efficient and is better organized with all the things in one place.
Syntax for the SSH Command in Linux
The best way to understand any command is through understanding it’s syntax. Here is how the syntax for the ssh command in Linux looks like.
ssh [option] [user]@[server_address]
Here, the server address can be either the address of the remote host which you wish to connect or it can be the IP address of your remote host. The ssh command in Linux allows several options to dictate how you connect to a remote host. Here is a list with some of the commonly used options offered by the ssh command in Linux.
| Option | Effect |
| -4 / -6 | Specify the ssh command that only IPv4(for -4) / IPv6 (for -6) addresses are permitted while creating an ssh connection. |
| -A | Specify the ssh command that authentication agent connection forwarding should be enabled while creating an ssh connection. This option should be used with caution. |
| -a | This option is used to specify the ssh command that authentication agent connection forwarding should be disabled while creating an ssh connection. This is the default option for the ssh command. |
| -C | Enable data compression while connecting over SSH. This can be helpful in case you are using a sluggish network. |
| -E LogFileName | Output the debug log to the specified output file |
| -p PortNumber | Specify a custom port number when the remote SSH server is not listening on the default port |
For the most part, you’ll never use anything apart from the options listed above because we just want to get a secure connection to a remote computer, and these options will help you achieve the result.
Using the SSH Command
Now that we have a solid foundation built for what the ssh command is and the different options available for use, we can move on to using the command on our system to connect to a remote host.
Note that to use ssh commands in Linux, the host system is required to have a running ssh server and the required ports should be open for incoming connections.
1. Accessing a remote host
The most basic use of the ssh command in Linux is to connect to a remote host. For this tutorial, we will use the user shell service offered by Rebex. The command should look like the following.
- Username: demo
- Password: password
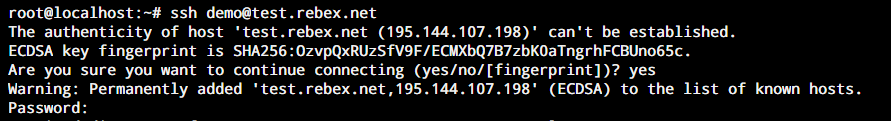
When you connect with a server for the first time, you would be asked if you wish to save the host fingerprint. Every host has a unique fingerprint. The fingerprints for all the known hosts for your system is stored at the ~/.ssh/known_hosts file. Enter ‘yes’ to save the remote host’s fingerprint. You would be then prompted to enter your password.
2. Connecting Over SSH on a Different Port
You wouldn’t always wish to route all your ssh traffic through port 22. Hence, it makes sense to be able to use a different port to connect to a remote host. Let’s now connect to a different server that allows connections on port 2222. However, this time we would use the port 8080 for our connection. Enter the following command in your terminal to do so.
ssh -p 2222 [email protected]
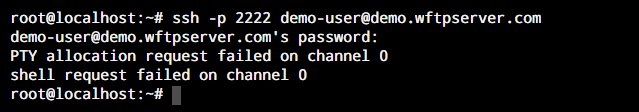
Note: In case of this testing server, it’s okay if you see a request failed for accessing the shell like in the screenshot above. It’s a public server and it wouldn’t make sense for security, to give access to a shell interface on the web. If you connect to a server that you know of, you’ll have the shell of the remote machine.
3. Execute commands on a remote server
Once you are connected to a remote host with the ssh command in Linux, you can use any commands allowed on the terminal. What makes it different then? Well, in this case, the commands you use will be executed on the remote host, not on your local machine. This allows you to access a machine even if you are not physically present at its location. This applies to every command available to you in the command line.
Conclusion
The ssh command is used to connect to remote hosts over the network. While telnet is available, ssh is much more secure than other protocols due to its encryption. We hope this tutorial was able to help you understand the ssh command in Linux. In the upcoming tutorials, we’ll cover how to setup password-less login for SSH servers that you connect to frequently.
